Overbuild for Microsoft#
VOSS provides an overbuild tool for each of:
Overbuild with Microsoft enabled (not Microsoft Defender)#
Overview#
The Overbuild feature enables Provider and Reseller administrators to integrate existing, deployed Microsoft tenants into VOSS without re-provisioning, unless required.
Important
It is recommended that VOSS Services are engaged during the initial use of the feature to help ensure optimized processes and guidance.
A Microsoft tenant in VOSS shows the combined and specific details of a MS Office 365 and MS Teams tenant.
Overbuild tools help the administrator manage Microsoft Tenant data synced from existing configurations.
While a Microsoft Tenant does not contain such VOSS components as a hierarchy or a user, the relationship with Microsoft tenant components makes it possible to, for example, create a VOSS user at a site hierarchy during the overbuild process. The necessary filters can be set up and workflows, macros, and brownfield move processes are available for this purpose.
Running overbuild the first time creates a schedule in the VOSS system that can be set up to run at a selected interval.
Overbuild logic for handling Microsoft users:
The synced in Microsoft tenant user is moved to the site based on the MS 365 model filter criteria selected for the site in the site overbuild defaults.
To allow this, ensure you select Include Site for Overbuild and Microsoft Users on the Overbuild Defaults tab in the Site Defaults.
To view the number of Microsoft users at the hierarchy level (MS 365 users, MS Teams users, and MS Exchange users), go to UC Overbuild Overview.
A Microsoft tenant user can be set up with services using Quick User.
In Microsoft environments, meeting rooms (device/msgraph/Room) are also processed during overbuild and automatically aligned with their associated Microsoft users.
Rooms are associated with users by matching the room email address with the user principal name (UPN), ensuring that when a Microsoft user is moved to a site, any associated rooms are moved to the same hierarchy level.
Note
Microsoft Guest users (Msol users external to the tenant) are synced in, but their group details (information about which groups they’re associated with) won’t be included in the sync.
Related topics
Configure a site’s overbuild defaults for Microsoft users#
This procedure configures a site’s overbuild defaults for Microsoft users.
Pre-requisite:
- Sync to customer then to site (Sync Microsoft users to sites)
If you want to move mailboxes to the site in the overbuild, ensure NDLs are configured for the overbuild by adding tenant details, including MS Exchange details.
All Microsoft elements must be moved to customer level in a sync before running the overbuild, which moves these elements to the sites.
To configure a site for overbuild:
Go to Site Defaults, and in the list view, click on a site to open its site defaults.
On the Overbuild Defaults tab:
Enable Include Site for Overbuild.
Define whether to create the internal number at the customer.
From Overbuild Device Control, choose Limit Moved Devices.
Enable Microsoft Users.
On the Move Filter Criteria tab, configure the following for Microsoft users:
From MS 365 User Model Filter Criteria, select the relevant filter. See Model filter criteria for further details.
Optionally, enable Move by Number.
Note
User data is moved to a site using Move by Number only if the synced in Microsoft Teams user’s LineURI matches a pre-loaded internal number at that site.
If you’ve selected a filter for MS 365 Model Filter Criteria and you’ve enabled Move by Number, overbuild first processes MS 365 Model Filter Criteria, and then processes Move by Number.
For more information about options on the Move Filter Criteria tab, see Site defaults.
Related topics
Run UC overbuild#
From Organization Selection, navigate to the relevant site.
Go to Run UC Overbuild.
In a Microsoft-only environment without MS Defender, select only Microsoft Users to include in the overbuild.
Note
This allows Microsoft users to move to the site. VOSS inspects the Microsoft user to check if it has MS Teams and MS Exchange, and moves these elements to the sites along with the user.
Save your changes to run the overbuild.
Note
For Microsoft Users*, the overbuild moves assigned numbers to the number inventory, flagged with the user’s name, location (customer or site), number status (Used when assigned, else, Available), and the relevant vendor (Microsoft, in this case).
The number management step occurs on sync, overbuild, as well as in a number audit. You can run a number audit anytime to verify that numbers are correctly flagged as used or available (via Number Inventory Audit Tool). See Number inventory audit for details.
Related topics
Run Overbuild with Model Filter Criteria (with Microsoft Defender)#
The Run Overbuild by Model Filter Criteria tool runs an overbuild with Microsoft Defender by model filter criteria. This tool enables moving resources across hierarchies based on selected model filer criteria instances where the model filter criteria Usage is set to Overbuild. For details, see Model filter criteria.
When Microsoft Defender is enabled via Enabled Services in the Global settings, then Microsoft Defender options are available on Run Overbuild by Model Filter Criteria.
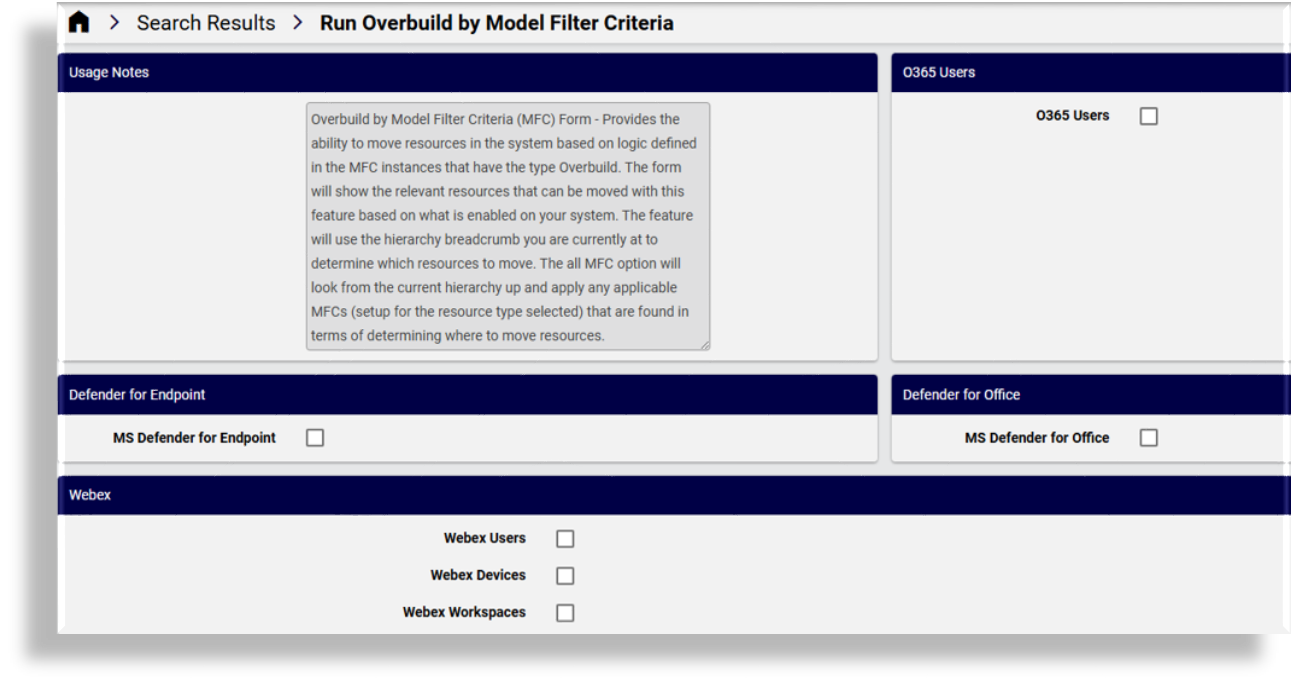
Microsoft Defender overbuild options allow the following:
Microsoft Defender for Endpoint
Moves Microsoft Defender for Endpoint device data and alerts down to lower hierarchy levels using model filter criteria.
Microsoft Defender for Office
Moves Microsoft Defender for Office attachments, links, and quarantine policies for Office down to lower hierarchy levels using model filter criteria.
Note
If you have the the UC Automation solution enabled in Global settings (via Enabled Solutions settings),
then Overbuild by Model Filter Criteria will not move device/msgraph/MsolUser and instead
moves this data by standard settings.
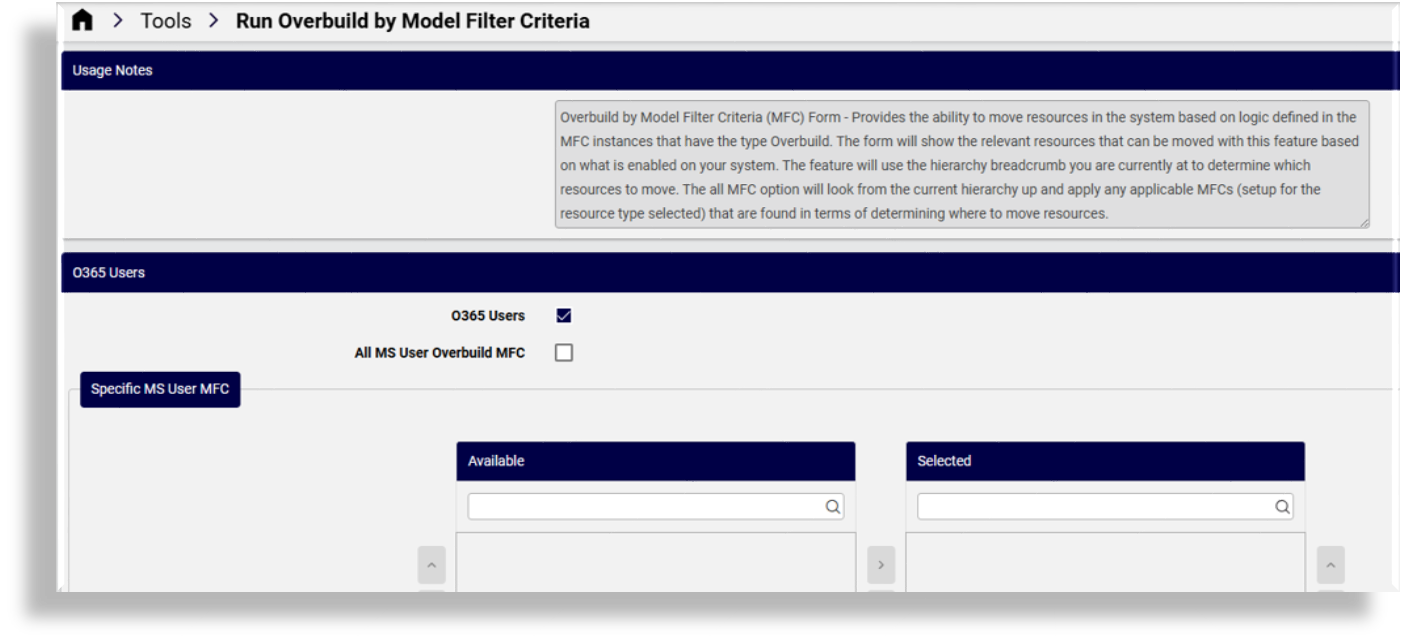
All or specific Microsoft user overbuild model filter criteria#
On Run Overbuild by Model Filter Criteria you can choose to run overbuild on either of the following:
All MS user overbuild model filter criteria (default)
The current hierarchy upwards (up to Provider level) is be checked for relevant MFCs that have been set up for the selected option. The listed instances are MFC instances where Automated Overbuild setting has been enabled.
Disabling All MS User Overbuild MFC on the form displays options for selecting specific Microsoft user model filter criteria.
Specific Microsoft user model filter criteria
When choosing to specify MFC instances, the form displays all MFC resources up to the
syshierarchy (including instances where the Automated Overbuild setting is disabled) on the Available pane. You can choose and move those instances to the Selected pane. The inclusion of instances with Automated Overbuild disabled here allows you to run selected MFCs without running them automatically by accident.
Note
The current hierarchy where the feature is used determines which resources specified in the MFC to move to the Target Hierarchy as specified in the MFC. This target hierarchy is thus not only limited to sites, but can be any created intermediate nodes representing an organizational structure.
Example hierarchies:
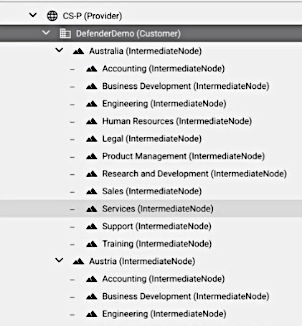
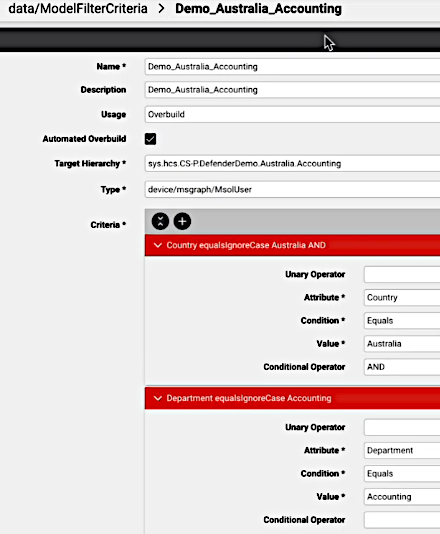
Example MFC:
When specific MFCs are selected, the overbuild move sequence will be carried out according to the MFC order in the Selected list (top-down).
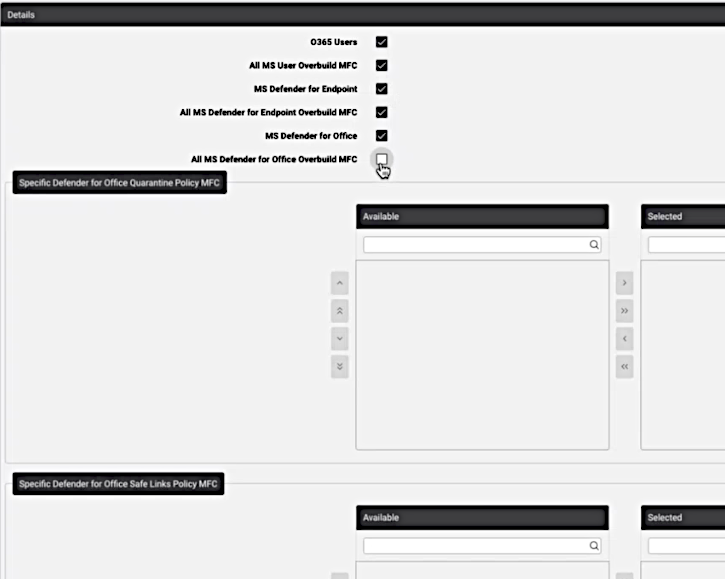
The following list shows overbuild options (not all may be enabled in your settings) and the conditions of their selection or de-selection:
O365 Users: checkbox. If checked, then either:
All MS User Overbuild MFC: checkbox (enabled by default)
or disabled, then:
Specific MS User MFC: transfer box
MS Defender for Endpoint: checkbox. If checked, then either:
All MS Defender for Endpoint Overbuild MFC: checkbox (enabled by default)
or disabled, then:
Specific Defender for Endpoint Machine MFC: transfer box
MS Defender for Office: checkbox. If checked, then either:
All MS Defender for Office Overbuild MFC: checkbox (enabled by default)
or disabled, then:
Specific Defender for Office Quarantine Policy MFC: transfer box
Specific Defender for Office Safe Links Policy MFC: transfer box
Specific Defender for Office Safe Attachment Policy MFC: transfer box
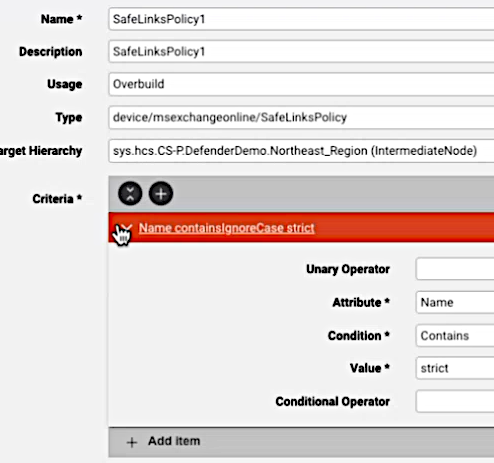
An example of option selection is show in the image below:
Microsoft Defender models and move rules#
This section describes which Microsoft Defender models are moved and the rules used to move them during overbuild. These settings are available in Overbuild Model Filter Criteria.
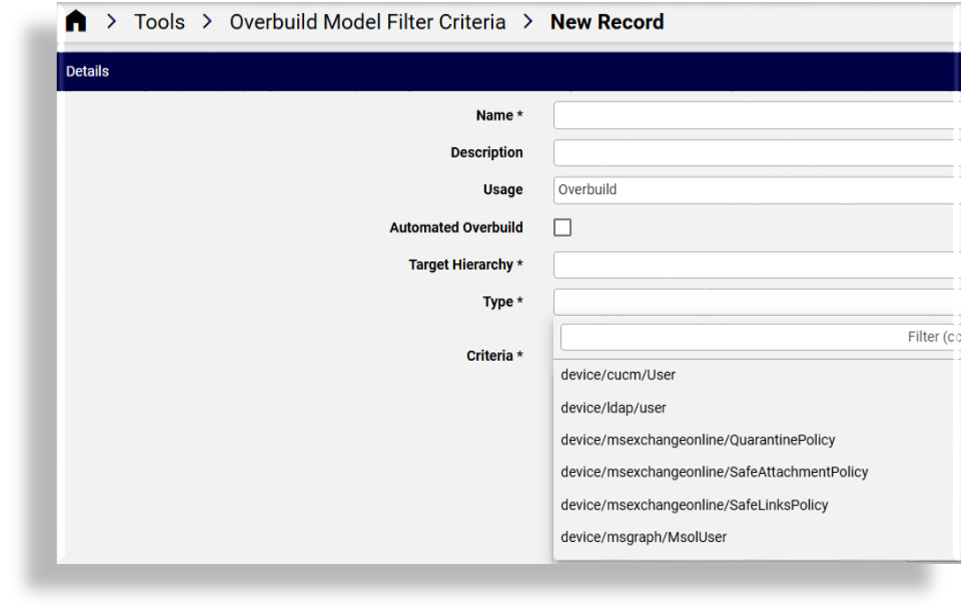
Model types
The Type drop-down selects model types to move via model filter criteria (MFC) for the policy where Usage is Overbuild to Target Hierarchy according to Criteria. See: Model filter criteria.
Office
When Microsoft Defender for Office is enabled as a service in global settings and the tenant configuration has synced collection data to the tenant hierarchy, overbuild moves attachments, links, and quarantine policies based on specified criteria for the model type:
device/msexchangeonline/SafeAttachmentPolicy: Move according to Model Filter Criteriadevice/msexchangeonline/SafeLinksPolicy: Move according to Model Filter Criteriadevice/msexchangeonline/QuarantinePolicy: Move according to Model Filter Criteriadevice/msexchangeonline/QuarantineMessage: Move to the first recipient address on each instance if theMsolUseris at a lower hierarchy.
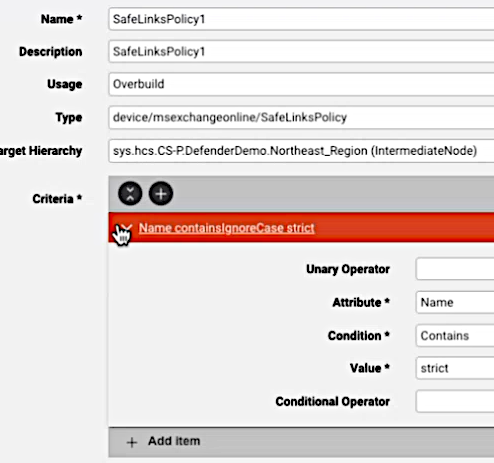
Example MFC instance:
Endpoint
When Microsoft Defender for Endpoint is enabled as a service in global settings and the tenant configuration has synced collection data to the tenant hierarchy, overbuild moves endpoint security data (attachments, links, and quarantine policies) according to the specified criteria for the model Type:
device/mssecurity/Machine: Move according to Model Filter Criteria instances that are set up.device/msgraphsecurity/Alert: Move Alert models based on hierarchy level of related Machine models at a lower hierarchy, since all the alerts follow a machine.device/msgraphsecurity/Incident: Move Incident models based on hierarchy level of related Alert models that are at a lower hierarchy, based on the incident IDs in the alert of the first matching alert. (Alert ID is referenced)
When Microsoft Defender for Endpoint is enabled, overbuild moves endpoint security data as a unit. Machines are moved using model filter criteria. All related alerts, incidents, and machine actions automatically follow the machine, preserving full remediation context at the target hierarchy.
Specifically, machine action data (
device/mssecurity/MachineAction) is automatically moved with its associated machine.
Related topics